Transcript
Spinning the Web: The Real Threat of Scattered Spider and How to Keep Families Safe Online
Author: Gursimar Singh Ply (VMGroup)
They call themselves ‘Scattered Spider’. They’re not hackers in dark basements; they are the new generation of cyber criminals and could be your teenager, or their classmates. And they’re being groomed and trained to target some of the world’s biggest companies using techniques a child can learn online e.g. YouTube. Here's what every family and teachers need to know about Scattered Spider: the cyber gang that's rewriting the playbook for online cybercrime.

Introduction
This article discusses the notorious cybercriminal collective known as Scattered Spider, with a particular focus on how teenagers are being groomed and recruited into their operations and the sophisticated criminal activities they conduct. The group represents a significant shift in the cybercrime landscape, demonstrating how young, English-speaking individuals are becoming increasingly central to major ransomware operations targeting Fortune 500 companies, critical infrastructure and healthcare. Recent arrests and ongoing investigations reveal a disturbing trend of teenagers as young as 16 years of age being drawn into high-stakes cybercriminal activities that have caused many hundreds of millions of Euros in damages to major corporations, with the group’s social engineering capabilities and decentralised structure making them particularly difficult for law enforcement to detect and combat effectively.
The following text is intended to help parents; care givers and educators understand the emerging risks associated with cybercriminal groups like Scattered Spider and the alarming ways in which young individuals are being recruited into their ranks.
As digital natives, teenagers may be more susceptible to online manipulation, lured by promises of status, financial gain or belonging. Understanding these motivations is critical not only to recognise early warning signs but also to intervene before curiosity turns into criminal involvement. By shedding light on how these groups operate and why they target young people, this article aims to equip adults with the knowledge needed to address the issue with both awareness and urgency.
What is Scattered Spider?
Scattered Spider, also known by multiple aliases including UNC3944, Octo Tempest, Muddled Libra and Star Fraud represents a unique phenomenon in the cybercriminal ecosystem 1. Unlike traditional cybercriminal groups that typically operate from Eastern Europe, Asia or other regions with limited law enforcement cooperation, Scattered Spider is composed primarily of young, native English-speaking teenagers based in Ireland, the United Kingdom and USA 2 &3. The group’s membership includes teenagers as young as 16 years, with many members being college-aged individuals in their late teens and early twenties 4.
What Makes Them Different?
Scattered Spider’s criminal activities have evolved significantly since the group’s emergence in mid-2022, demonstrating an increasingly sophisticated approach to cybercrime that maximises both financial gain and operational impact. The group initially focused on telecommunications firms, using various tactics to compromise accounts and systems. These included SIM swap scams, where criminals trick mobile providers into transferring a victim’s phone number to a new SIM card under their control, allowing them to intercept calls and messages. They also used multi-factor authentication (MFA) fatigue attacks, which involve repeatedly sending authentication requests to a victim’s device in the hope they will approve one out of frustration or confusion. Scattered Spider also carries out phishing campaigns; fraudulent attempts to obtain sensitive information through platforms like SMS and Telegram, often by posing as legitimate contacts or services to deceive victims.
These early activities serve as training grounds for young members to develop their social engineering skills and technical capabilities.
The group’s methodology centres on advanced social engineering techniques rather than traditional malware development, making their attacks particularly difficult to detect and prevent. They specialise in manipulating employees into unwittingly granting the attacker access to internal systems through convincing phone calls to corporate IT help desks. This approach has proven extremely effective as it bypasses many traditional cybersecurity defences that focus on detecting malicious software rather than social manipulation.
The group's English-speaking nature and Western origins set them apart from most major cybercriminal organisations, making their social engineering attacks particularly effective against English-speaking targets. This linguistic advantage allows them to conduct sophisticated phone-based social engineering attacks that would be difficult for non-native speakers to execute convincingly 7.The U.S. Federal Bureau of Investigation (FBI) and the Cybersecurity and Infrastructure Security Agency (CISA) have noted that the group's native English capabilities make their social engineering techniques especially effective and therefore dangerous 8.
Why Teenagers?
The grooming and recruitment of teenagers into cybercriminal groups like Scattered Spider reflects a complex interplay of the world wide web, technological proficiency, social dynamics, and knowledge gained about systemic vulnerabilities. This phenomenon is not merely a byproduct of individual delinquency but a calculated strategy by sophisticated criminal networks to groom and then exploit the unique advantages that young, tech-savvy individuals offer. Below, we dissect the motivations, mechanisms, and implications of this trend, drawing parallels to broader patterns in cybercrime recruitment.
The Digital Native Advantage
Teenagers today are digital natives, immersed in technology from an early age. Many develop advanced technical skills through gaming, coding and exploring online platforms. For instance, a 16-year-old member of the Lapsus$ group demonstrated exceptional aptitude by infiltrating companies like Microsoft and Nvidia, amassing $14 million through ransomware attacks 15. These skills when misdirected and exploited make teenagers valuable assets to groups like Scattered Spider which rely on expertise in cloud computing, social engineering and malware deployment.
The Gamification of Hacking
Online gaming communities often serve as training grounds for cybercrime. Communication Platforms like Discord and Telegram host forums where teenagers share modding tools, cheat codes and hacking techniques. The UK’s National Crime Agency (NCA) notes that 25% of gamers aged 10-16 engage in activities violating the UK’s Computer Misuse Act 1990 such as DDoS attacks or unauthorised account access 16. These low-level offenses initially perceived as harmless gaming exploits, normalise criminal behaviour and provide a pathway into more serious cybercrime.
Peer Validation & Online Reputation
For many teenagers, cybercrime is less about financial gain and more about social capital. A study by the UK NCA found that 70% of young hackers are motivated by the idea of a “collective of skilled individuals” that rewards members with status within their secretive online community for executing high-profile attacks, such as the 2023 breaches of MGM Resorts and Caesars Entertainment. This culture mirrors the dynamics of online gaming leaderboards, where achievements translate to clout, or notoriety within their peer group.
Curiosity & Moral Ambiguity
Adolescent curiosity often blurs the line between ethical exploration and criminal activity. The case of Kristoffer von Hassel, who bypassed parental controls on an Xbox at age 5, illustrates how early technical experimentation can evolve into hacking 17. Many teenagers view cybercrime as a victimless endeavour, particularly when targeting large corporations and this perception is promoted by the likes of Scattered Spider to overcome objections of their new recruits. This perception is exacerbated by the anonymity of online platforms, which insulate users from the real-world consequences of their actions.
Red Flags & Tips for Parents
Parents should be alert to certain behaviours that may indicate a teenager’s curiosity about or involvement in cybercrime. A sudden interest in “ethical hacking” tutorials or participation in dark web forums can be an early indicator. Likewise, unexplained income such as new cryptocurrency wallets or sudden spikes in gaming credits may point to ill-gotten gains from illicit activities. Another warning sign is a child becoming unusually withdrawn during conversations about their online habits. According to UK’s National Crime Agency (NCA), 61% of young hackers start with what seem like harmless activities, such as modifying video games.
Protecting Your Child: A Four Point Action Plan
Talk Early, Talk Often
Open, ongoing conversations are key. Help your child understand the real-world consequences of cybercrime. Hacking into corporations or databases is not a victimless act and it can have serious legal and ethical consequences. Give examples using current events like the breaches of companies such as Co-op or Harrods as conversation starters to reinforce these points.
Monitor Digital Footprints
While respecting your child’s privacy, take proactive steps to monitor their activity. Enable parental controls on home routers and devices but avoid heavy-handed snooping. Be aware of the use of encrypted messaging apps like Signal or Telegram as these are the tools that hacking groups like Scattered Spider often use to communicate, as the communications are encrypted and as a result evade detection.
Redirect Technical Curiosity
If your child shows an interest in coding or cybersecurity, channel that energy positively. Encourage participation in coding clubs or structured ethical hacking programmes such as CyberFirst. This will legitimise their interest while also opening doors to a career in cybersecurity, a sector in Ireland experiencing significant growth. In 2024, the industry in Ireland employed over 8,000 professionals and contributed approximately €2.7 billion in revenue.
By the end of 2025, the cybersecurity market globally is projected to reach a revenue of US$602.98 million, with a compound annual growth rate (CAGR) of 5.74% expected through 2030. Cyber Ireland's roadmap aims to employ 17,000 professionals and generate €2.5 billion in gross value added annually by 2030. This growth is driven by Ireland's strategic position as a hub for multinational cybersecurity firms, a strong pipeline of STEM graduates, and supportive government initiatives 18.
Globally, the cybersecurity sector is also experiencing robust expansion. In 2025, the global cybersecurity market is projected to reach US$202.98 billion, with a CAGR of 7.58% expected through 2029. By 2034, the market size is anticipated to grow to US$878.48 billion, reflecting a CAGR of 12.60% from 2025 to 2034. This global growth is driven by increasing cyber threats, digital transformation across industries, and rising awareness of the importance of cybersecurity.
Recognise Behavioural Shifts
If you notice changes in your teenager's behaviour that may indicate involvement in online communities with potentially harmful influences, such as increased secrecy or unexplained absences, it's important to take proactive steps. One such community is "The Community," which may be linked to hacker networks like Scattered Spider. If you suspect your child may be engaged in illegal activities, consider reaching out to government initiatives for guidance and support.
In Ireland, the National Cyber Security Centre (NCSC) is a government agency responsible for advising and informing on current threats and vulnerabilities associated with network information security. They provide guidance to citizens and businesses on major cybersecurity incidents and are part of the Department of Justice, Home Affairs and Migration.
The NCSC also encompasses the State's National/Governmental Computer Security Incident Response Team (CSIRT-IE), which helps in responding to cybersecurity incidents at a national level. For more information or to report a cybersecurity incident, you can visit their official website: https://www.ncsc.gov.ie/
Law Enforcement Response & Ongoing Challenges
Law enforcement agencies in the United States, United Kingdom, Ireland and Europe have significantly intensified their efforts to combat Scattered Spider, resulting in multiple high-profile arrests throughout 2024 and 2025 10. The National Crime Agency (NCA) in the UK has named Scattered Spider as a key focus of their investigation into recent retail sector attacks, marking the first time police have publicly confirmed they are actively investigating the group’s involvement in UK incidents 11.
Law enforcement investigations have revealed that several high-profile members of the group were arrested while still in their teens or early twenties. Tyler Robert Buchanan, a 23-year-old from Scotland who U.S prosecutors claim is a leader of Scattered Spider was arrested at a Spanish airport in June 2024 5. More recently, a 17-year-old from Walsall, UK was arrested in connection with group’s activities, highlighting the youth of many participants 6.
Despite these law enforcement successes, the decentralised nature of Scattered Spider presents ongoing challenges for investigators and prosecutors. The group's structure as a loose network of individuals operating across multiple jurisdictions makes it difficult to dismantle the entire organisation through targeted arrests 11. Even when key members are arrested, the group's flexible structure allows remaining members to quickly reorganise and continue operations with new recruits 12.
The international nature of the group's operations further complicates law enforcement efforts, as members based in different countries require complex extradition proceedings and international cooperation agreements. Tyler Buchanan's case exemplifies these challenges, as he was arrested in Spain but required extradition to the United States for prosecution, a process that took several months to complete 13.
The FBI and CISA have responded to the Scattered Spider threat by issuing detailed advisories outlining the group's tactics, techniques, and procedures, while providing recommendations for organisations to defend against their attacks 8. However, the social engineering focus of the group's attacks means that traditional technical defences are often insufficient, requiring organisations to invest heavily in employee security awareness training programs.
Current Threat Landscape & Future Implications
Silent Push research indicates that Scattered Spider remains highly active in 2025, with the group continuing to develop new capabilities and target high value organisations across multiple sectors 13. Recent intelligence suggests the group is targeting services including Klaviyo, HubSpot, and Pure Storage, while brands such as Nike, Louis Vuitton, Credit Karma, and News Corporation have been identified as potential targets 13.
The group's acquisition of domains previously owned by major technology companies, such as the twitter-okta[.]com domain formerly associated with Twitter/X, demonstrates their strategic approach to establishing infrastructure for future attacks 13. This domain acquisition strategy suggests long-term planning and investment in attack infrastructure that could be used for years to come.
Cybersecurity researchers are tracking five unique Scattered Spider phishing kits that have been in use since at least 2023, with some kits receiving regular updates and improvements 13. The evolution and refinement of these tools indicate that the group is continuously improving their capabilities and adapting to defensive measures implemented by target organisations.
The emergence of new variants of remote access tools, including updated versions of Spectre RAT used by Scattered Spider, suggests that the group maintains relations with skilled malware developers who can create custom tools for their operations 13. This technical capability, combined with their social engineering expertise, makes them a particularly formidable threat to organisations across all sectors.
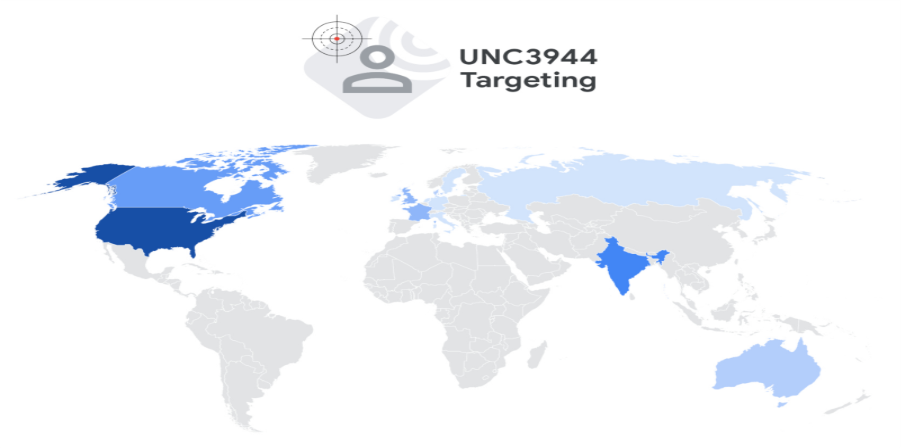
Source: Defending Against UNC3944: Cybercrime Hardening Guidance from the Frontlines | Google Cloud Blog
Breaking Down the Tech
Scattered Spider tend not to use sophisticated technology or cyber-attacks but simple social engineering techniques and tricks to infiltrate a system. Let's look at some of those techniques and try to understand how they work.
Social Engineering
Social engineering attacks are based on manipulating people into sharing information that they wouldn’t normally and shouldn’t share, downloading software that they shouldn’t download, and viewing websites they shouldn’t visit 7. Social Engineering uses psychological manipulation and exploits “the human factor”; human error or weakness, rather than technical or digital system vulnerabilities; it is sometimes called “Human Hacking”.
The teenagers and young adults within Scattered Spider have developed remarkably sophisticated social engineering capabilities that rival those of state-sponsored threat actors 8. Their native English-speaking ability provides a significant operational advantage when targeting Western corporations as they can conduct convincing telephone-based social engineering attacks without the linguistic barriers that often expose foreign threat actors 9.
The group’s social engineering playbook typically begins with extensive reconnaissance of target organisations, rather information about company structure, employee names and internal processes from public sources and previous breaches 9. Armed with this information, group members call corporate IT help desks impersonating employees who need urgent assistance with account access or technical issues. Their youth and familiarity with contemporary technology terminology makes these impersonations particularly convincing to help desk staff.
A particularly effective technique employed by the group is “push bombing” or multi-factor authentication (MFA) fatigue attacks, where they repeatedly send authentication requests to a target’s mobile device until the victim approves the request simply to stop the notifications 8. This technique exploits human psychology and the tendency of users to approve authentication requests without careful consideration, especially when bombarded with multiple requests.
For example, in August 2023, Scattered Spider attackers targeted Caesars Entertainment, a prominent U.S casino and hospitality company. Posing as an internal IT user, they contacted an outsourced help desk and successfully convinced staff to reset login credentials. This breach enabled the attackers to access sensitive customer data, including driver’s license and possibly Social Security numbers. Subsequently, Scattered Spider demanded a $30 million random, which Caesars negotiated down to $15 million. This incident gives a perfect example of the effectiveness of social engineering tactics in bypassing security measures and highlights the significant risks posed to organisations relying on third-party IT support services.
Because these methods rely on human error rather than technical flaws, they are harder to detect and stop with traditional cybersecurity tools. That’s why security awareness training are just as important as firewalls and antivirus software, especially in the organisations where any employee can be a potential target.

Source: What-is-Social-Engineering-and-What-are-the-Red-Flags-infographic-1024x1024.jpg (1024×1024)
Ransomware Deployment & Double-Extortion
Once deep inside a network, Scattered Spider often teams up with ransomware providers like DragonForce, Qilin or ALPHV/BlackCat. In the M&S attack, they deployed DragonForce to encrypt VMware ESXi servers and exfiltrated customer and operational data, threatening to leak it unless a ransom was paid. The disruption to the business is currently estimated at £300 million and counting in financial disruption.
Double extortion occurs when the cybercriminal demands a ransom in exchange for the decryption key, without which the victim organisation is unable to access their data. The second part of the Double Extortion occurs when the cybercriminal threatens to release into the public domain the exfiltrated (stolen) data unless a further ransom is paid in exchange for the return of that data.
There are other elements to the financial pain experienced by the victim organisation; firstly, the rebuild cost of replacing network infrastructure and reimaging the desktops and laptops. This is a necessary step as there is no way of knowing if the cybercriminal remains lurking on the organisations network, ready to strike again. Secondly, the potential fines imposed by the respective regulators because of the data breach. This is particularly true in cases where the victim organisation is proven to have failed in their compliance responsibilities with the likes of GDPR, for example. The Data Protection Commission in Ireland may impose fines of up to 200 million euros, or 4% of global turnover, whichever is greater, per data breach.
Credential Theft & Privilege Escalation
After gaining initial access to an organisations network often via MFA fatigue, SIM-swapping (convincing telecom providers to assign a victim’s phone number to the attacker’s SIM to bypass SMS-based MFA) or spear phishing (targeted deceptive emails designed to steal passwords or other sensitive information), Scattered Spider focuses on stealing credentials from privileged accounts. These might include IT admins or vendor support teams.
During a February 2025 attack on Marks & Spencer (M&S), The group acquired the domain controller’s NTDS.dit file, which is a critical database used by Windows Active Directory to store information about all user accounts, including their password hashes which are encrypted versions of passwords that are not stored in plain text but converted into scrambled strings using cryptographic algorithms. These hashed passwords cannot be easily read, but if obtained, they can sometimes be cracked or used in further attacks.
In the M&S case they cracked those hashes to escalate and move laterally across the network, sidestepping cybersecurity controls. Throughout the process, they rely on native system management tools like PowerShell and PsExec a classic “Living off the land” tactics to avoid detection.
Supply Chain & Remote Access Tool Exploitation
Scattered Spider often targets third-party vendors and remote management platforms to widen their reach and sometimes those behind the screens are surprisingly young. In spring 2025, they infiltrated retailers like M&S, Co-op and Harrods not by going direct, but by compromising a third-party contractor’s account. That contractor’s access credentials became the route by which the attack unfolded, which disrupted online ordering and services for weeks. It’s a reminder that even a single compromised User Account, or vendor can open the door to huge disruption in any organisation, not only some of the best-known house-hold brand names and leading organisations.
Beyond this, the group abuses trusted Remote Monitoring and Management Tools including AnyDesk, TeamViewer, Zoho Assist, RustDesk and others to maintain stealthy, ongoing control over compromised systems. These are legitimate tools used every day in IT support, but when hijacked, they become invisible conduits for the attackers. In multiple incidents, Scattered Spider even exploited an old Intel Ethernet driver vulnerability (CVE-2015-2291), injecting a malicious driver to disable security tools, an advanced trick known as “Bring Your Own Vulnerable Driver” (BYOVD).
By focusing on third-party supply-chain weaknesses and established administration channels, Scattered Spider gains persistent, hidden access and their youthful operatives often learn and adapt fast to exploit their network access. In one case, they posed as help-desk vendors to deliver Remote Monitoring and Management (RMM) software, a type of tool commonly used by IT professionals to access and control systems remotely. They delivered it through spear phishing, which is a targeted form of phishing where attackers send carefully crafted messages to specific individuals to trick them into clicking a malicious link or downloading harmful software. This gave the attackers remote access with minimal suspicion. As a result, they could quietly enter the network, stay hidden for longer periods, and collect valuable sensitive data long after the initial social engineering attack, where someone is manipulated into giving away sensitive information, had been forgotten.

Source: Mirage Security - Scattered Spider Attacks: Timeline, Tactics, and Defense Tips
Layered Defence Against Scattered Spider for Corporations
Scattered Spider thrives on social engineering and help-desk manipulation including SIM-swapping, vishing, MFA fatigue and credential resets giving attackers a way to talk their way through your company’s front door. Here’s a consolidated strategy to fight back:
Phishing Resistant & Device Bound MFA
Scattered Spider relies heavily on bypassing weak multi-factor authentication methods like SMS, one-time codes and push notifications. By adopting phishing-resistant, device-bound MFA such as FIDO2 security keys, passkeys or PKI-based tokens you eliminate the shared secret mechanism the attackers seek to exploit. These measures prevent adversaries from using man-in-the-middle phishing tools like EvilGinx because the hardware keys verify the domain before signing and the private keys never leave the device.
Enforcing device compliance through Mobile Device Management (MDM) or conditional systems access policies ensures that only trusted and properly managed devices can log in, adding an important layer of security. MDM allows organisations to monitor, control, and secure employee devices used for work, helping to reduce the risk of unauthorised access. Without these measures, attackers can bypass weak multi-factor authentication (MFA), a security method that requires users to verify their identity using a second step such as a code sent to their phone. This can result in full account takeovers through techniques like SIM swaps or MFA fatigue attacks.
Scattered Spider constantly abuses help desk processes, impersonating employees to reset credentials or remove MFA protection. According to the FBI, they have tricked IT staff into adding unauthorised MFA devices or approving resets by creating urgency and spoofing internal communications channels. To prevent this, help desk agents must follow rigorous verification processes: call back on known number (with awareness of SIM-swapping risk), use secure video ID checks and require multi person approvals especially for privileged accounts. Ignoring these safeguards allows attackers to impersonate support staff, escalate privileges and pivot across systems unseen.
Continuous Monitoring & Logging
Technical stealth is a hallmark of Scattered Spider’s tactics, techniques and procedures, commonly referred to as TTPs. These describe the standard behaviours, tools and methods used by a threat group during different stages of an attack. Instead of leaving behind suspicious files, the group makes use of legitimate remote access tools and scripts to avoid detection.
Strong defence involves collecting logs from identity providers, virtual private networks (VPNs), and monitoring tools such as endpoint detection and response, known as EDR, and extended detection and response, known as XDR. EDR focuses on identifying and reacting to threats on individual devices such as laptops or servers. XDR expands this by combining information from devices, networks and cloud services to give a broader view of security activity.
Network performance monitoring can also help by identifying unusual traffic patterns that may indicate malicious activity. Setting alerts for unexpected multi-factor authentication enrolments, unauthorised use of privileged accounts and suspicious remote tool activity is vital. These measures help to detect what are known as living off the land attacks, where attackers use built-in or trusted tools to blend into normal operations. Without these defences, data theft and account abuse can occur without being noticed until serious damage has already been done.
Security Awareness Training, Red-Team Testing & Threat Intelligence
Humans (the “Human Factor”) remain the weakest link in security and are therefore the most targeted strategy for Scattered Spider. Tailored training, including simulated vishing and phishing attempts, as well as help-desk impersonations, is essential to help staff recognise, verify or escalate abnormal requests.
Phishing is a form of social engineering where attackers send fraudulent emails that appear to be from legitimate sources to trick people into revealing sensitive information, such as passwords. Vishing is a similar technique carried out over the phone, where attackers pose as trusted individuals to manipulate victims into sharing information or performing actions.
Red team exercises are simulated cyberattacks carried out by internal or external security professionals who behave like real attackers to test how well an organisation’s defences respond in practice.
Tabletop drills are practice sessions where staff gather to talk through how they would handle particular security incidents. Instead of performing technical tasks, the team discusses step-by-step what actions they would take if faced with a real situation. These drills are especially important for dealing with high-risk events, like requests to reset passwords or increase user permissions, especially when those requests come under pressure or seem unusual. The goal is to make sure everyone understands their role and can respond quickly and correctly when it really matters.
Supporting these efforts, active threat intelligence such as monitoring for new phishing websites, conversations on the dark web and newly developed attack tools can provide early warning and real-world insight before large-scale campaigns begin. Without these protections, social engineering threats continue to bypass defences at an alarming rate.
How VMGroup Helps Defend Organisations
VMGroup reinforces layered defences by running realistic Scattered Spider-style red-team assessments to test helpdesk and password-reset protocols. VMGroup’s globally recognised cybersecurity professionals, with over 100â¯years’ experience, guide the implementation of device bound multifactor authentication and conditional access policies. These measures ensure only secure and managed devices can access sensitive systems. VMGroup’s proactive monitoring services detect and alert on unusual password resets, use of remote access tools, and privilege escalations, providing early warnings of potential compromise.
VMGroup’s custom Security Awareness Training is informed by real-world phishing, vishing and social engineering scenarios, helping staff spot and question suspicious requests. This training pairs with threat-intelligence and dark web monitoring to track emerging risks such as new phishing domains, attacker tools and exploit kits enabling organisations to anticipate threats rather than simply respond.
Backing this expertise is a comprehensive digital-forensics and cyber incident-response capability. VMGroup’s forensics team delivers 24/7 incident response, digital forensic investigations, data recovery, expert-witness testimony and eDiscovery support, across sectors from FTSE100 organisations to SMEs across Ireland, the UK, Europe, Africa and the UAE. VMGroup’s ISO certified audits and compliance services including GDPR and ISO27001 readiness ensure legal and regulatory adherence.
References

